How Field Service Businesses Can Keep Customer Data Safe on Every Job

Your techs carry more than tools. On every job, they handle customer names, home addresses, payment details, and sometimes access codes. They pull all of it up on phones and tablets, often on public Wi-Fi.
That is a real risk. And most small field service businesses do not think about it until something goes wrong.
The numbers are clear: 46% of all data breaches hit businesses with fewer than 1,000 employees. Small businesses get 350% more scam attacks than large ones. You are not too small to be a target. You are exactly the right size.
This guide covers what you need to keep your data safe while your team works in the field. No tech jargon. No big IT team needed.
1. Why Is Field Data More at Risk Than Office Data?
Office data sits behind a firewall, on a locked network, in a building you control. Field data does not have any of that.
Your techs are always on the move. They log in from parking lots. They connect to customer networks. They send invoices from personal phones.
Every one of those moments is a gap a hacker can use.
2. What Customer Data Are You Actually Storing?
Most field service owners do not realize how much sensitive data they hold. Think about what your techs see and store on every job:
-
Customer home addresses: exact places where people live and work.
-
Payment details: credit card numbers and bank info for repeat billing.
-
Access codes and lockbox numbers: sometimes full security system access.
-
Service history: what gear customers have, when it was last fixed, and any known issues.
-
Phone numbers and email addresses: direct contact info for every customer.
For business accounts, it gets more serious. HVAC techs often connect to building systems that control heat, cooling, and door access.
The most well-known case: the 2013 Target breach. Hackers got into Target through a stolen login from Fazio Mechanical, an HVAC company. The result: 40 million credit cards stolen and $202 million in damages. It all started with one field service company's weak security.
3. Common Threats Field Workers Face
Before we get into fixes, here is what you are up against.
1. Public Wi-Fi Risks
Your tech connects to Wi-Fi at a job site or a coffee shop. A hacker on the same network can read data that is not locked down. This is called a man-in-the-middle attack. The fix is easy: always use a VPN. A VPN scrambles your data so others cannot read it.
2. Phishing Emails and Texts
A fake email looks like it came from your bank, your supplier, or a customer. Your tech clicks a link, types in their login, and hands a criminal full access to your system. Phishing causes 90% of data breaches. Small business staff get 350% more of these attacks than people at big companies.
3. Lost or Stolen Devices
70 million devices are stolen each year. Only 7% are ever found. If a tech's phone or tablet goes missing without a lock on it, every customer record it touched is now at risk. More than 41% of all data breaches start with a lost or stolen device.
4. Shared Passwords and Weak Logins
This is the dirty secret of small trades businesses. Whole crews share a single login for the field service app. One password that everyone knows.
81% of company data breaches come from bad password habits. And 94% of passwords get reused across accounts. If one login gets stolen, everything linked to it is at risk.
5. Location Tracking
Every device online gives off location data. Your techs' routes, your customer locations, and your job schedule can all be tracked by bad actors if your network is not locked down.
6. Threats from Inside
Not every threat comes from outside. A former employee with active access, a tech who shares customer info by mistake, or someone who takes a photo of sensitive data. Always track who has access to what. Remove accounts the day someone leaves.
4. Train Your Team First
Here is the hard truth: your techs are the biggest risk to your data. Not because they are careless. Because 68% of all breaches start with a simple human mistake.
Only 39% of small businesses offer any security training. And 58% of small business staff cannot spot a phishing email.
The good news? Training works fast. After one session, staff are 75% less likely to fall for a phishing scam. Good training cuts overall risk by 70%.
What to Cover in Training
-
Phishing: how to spot fake emails, bad links, and urgent requests for login details.
-
VPN use: when and how to turn it on. Make it a rule, not a choice.
-
Device safety: Do not leave tablets in plain sight in your truck. Use a screen lock. Never log in on a customer's personal Wi-Fi.
-
Login habits: never share passwords. If someone leaves, cut their access that same day.
-
Reporting: Make it easy for techs to flag something odd without fear of blame.

Run training four times a year. Studies show staff forget what they learned within four months.
5. Fix Your Password Problem
If your whole crew shares one login, that is a serious gap. And you are not alone. Most small HVAC, plumbing, and electrical shops work this way.
When a shared password gets stolen, you cannot tell which account was hit. You cannot track who saw what. And if a tech leaves on bad terms, they still have full access.
Simple Fixes That Make a Big Difference
Give every tech their own login. Most job management apps support this at no extra cost.
Use a password manager like Keeper, 1Password, or Bitwarden. These tools store strong passwords so techs do not have to remember them. Many are free for small teams.
Cut access the day someone leaves. Do not wait until the following week.
Turn on two-step login (MFA) for every app. Only 20% of small businesses do this. It blocks 99% of automated attacks.
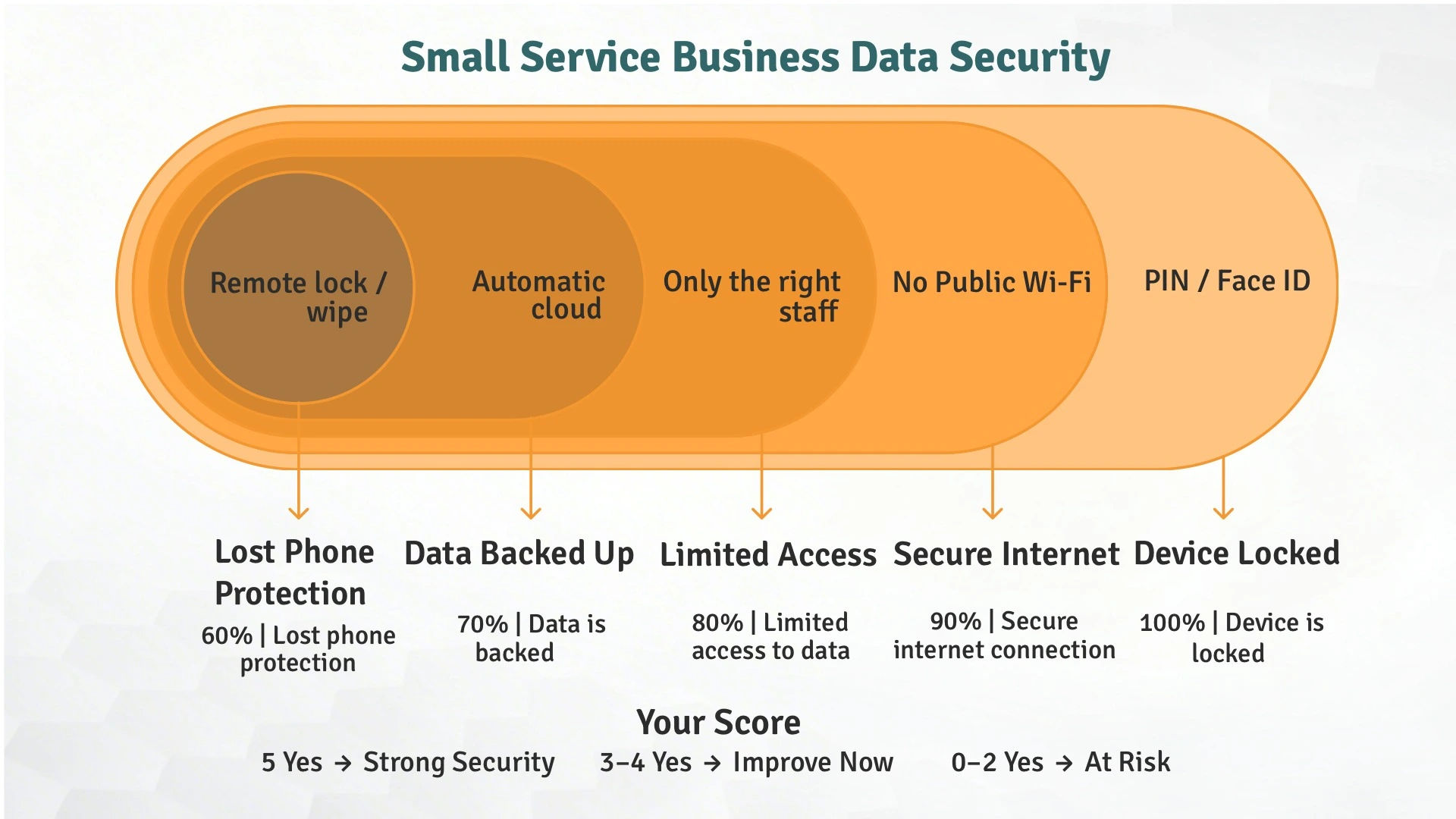
6. Key Security Steps for Field Teams
1. Always Use a VPN
A VPN locks your internet connection. Even on a public network, a hacker cannot read your data. Every tech should have a VPN on their work device and know to turn it on before opening any business app.
Business VPNs start at around $8 per user per month. That is less than a coffee a week.
2. Two-Step Login (MFA)
MFA asks for a second proof of who you are beyond a password. A code sent to your phone, a fingerprint, or an app. Even if someone steals a password, MFA stops them from getting in.
Turn it on for every business app: your job management software, email, accounting, and supplier portals.
3. Lock Down Your Data
Encryption scrambles data so only the right person can read it. You need two kinds:
In transit: protects data as it moves between devices. A VPN handles this. Look for 'TLS' or '256-bit encryption' when picking any business software.
At rest: protects data saved on a device. Turn on full-disk encryption on all work phones and tablets. On iPhones, this is on by default. On Android, go to Settings > Security > Encryption.
4. Use Cloud Storage, Not Local Storage
Data saved only on a device is gone if that device is lost or broken. Cloud storage means your data is always backed up and safe, even if a device goes missing.
Make sure your cloud provider uses strong encryption and lets you set access by role.
5. Limit Who Can See What
Not every tech needs to see every record. Your dispatcher does not need payment details. A junior tech does not need admin access to your accounting software. Set access based on what each person actually needs. Review it every six months.
6. Keep software updated
Old software has known gaps that hackers target. Turn on auto-updates for all devices and apps. Do not skip them.
7. Avoid Public Charging Stations
USB ports at airports, hotels, and coffee shops can be rigged to load bad software on your device. The FBI calls this juice jacking.Use a wall charger or power bank instead.
7. Mobile Device Management for Field Teams
Your techs use phones and tablets for work orders, customer contact, and job photos. Those devices are now part of your business systems, even if you have never thought of them that way.
Mobile Device Management (MDM) software lets you control and secure all your devices from one place. No IT degree needed.
What MDM Can Do
-
Remote wipe: if a device is lost or stolen, delete all business data from anywhere.
-
Force encryption: make sure every device is locked before it can access company data.
-
App controls: choose which apps can be installed and block risky ones.
-
Push updates: send security fixes to all devices at once.
Keep work and personal data apart: store company data in a safe space, away from personal apps. Low-cost MDM options include Miradore (free for up to 50 devices), Jamf Now (free for 3 devices), and Hexnode UEM (from $1.20 per device per month).
8. The BYOD Problem: When Techs Use Personal Phones
Most small field service businesses cannot give every tech a work phone. So techs use their own. This is called Bring Your Own Device, or BYOD.
The risk: 50% of companies that allowed BYOD had a breach through a personal device. Yet only 32% of those businesses set proper rules.
You do not have to ban personal phones. You just need a policy.
A Simple BYOD Policy for Small Trade Shops
-
Require a PIN or fingerprint lock on any device used for work.
-
Require VPN use before opening any business app.
-
Have techs sign a one-page agreement that covers data ownership and your right to wipe work data if they leave.
-
Use a work profile: Android and Apple both let you create a separate space for work data, away from personal apps.
-
Cut access the moment someone leaves.
9. How the Right Job Management Software Protects Your Data
A cloud-based field service management (FSM) platform is one of the best security tools you can buy. Most owners think of it as a scheduling app. It is also a key part of keeping your data safe.
Paper vs. Digital: The Security Case
Paper work orders sit in truck glove boxes, get left at job sites, and end up in dumpsters with customer names in plain sight. There is no way to track who saw them or destroy them from a distance.
Digital work orders stored in a secure FSM platform give you:
-
Login controls: only approved users can see records.
-
Role-based access: techs see only what they need for their jobs.
-
Auto cloud backup: data is safe even if a device is lost or broken.
-
Full audit trail: you can see who looked at or changed any record and when.
-
Encryption: all data are locked in transit and at rest.
What to Look for in a Secure FSM Platform
Before choosing any FSM software, ask these questions:
-
Does it use 256-bit encryption?
-
Is it SOC 2 certified?
-
Does it let you set access by role?
-
Does it back up data to the cloud?
-
Does the vendor have a clear policy for fixing security issues?
Field Promax was built with these security requirements in mind. Every work order, customer record, and technician note is stored in an encrypted cloud environment with role-based access, full audit trails, and automatic backups.
.png?updatedAt=1747763704661)
10. Ransomware: The Attack That Can Shut You Down Overnight
Picture a Monday morning in July. Your dispatcher logs in to start the day. Instead of your schedule, there is a message: your files are locked. Pay up to get them back.
Every file is gone. Schedules. Customer records. Your billing software. Your whole business stops on the hottest day of the year.
This is not made up. 82% of ransomware attacks hit businesses with fewer than 1,000 employees. Ransomware was part of 44% of all breaches in 2024. The average cost to recover: $2.73 million.
How Ransomware Gets In
-
Phishing emails: a fake invoice or delivery notice that looks real.
-
Weak remote access: tools like TeamViewer or RDP without two-step login are an easy target.
-
Old software: known gaps in apps that have not been updated.
-
Stolen passwords: from a tech who clicked a bad link months ago.
How to Guard Against Ransomware
Back up your data and keep those backups off your main network. Follow the 3-2-1 rule:
-
Three copies, two storage types, one offsite or cloud backup
-
Use two-step login on everything, especially remote access tools
-
Train your staff to spot phishing, your first line of defense.
Have a plan before it happens. Know who to call and which systems to restore first.
11. Secure Your Invoices and Customer Messages
.webp?updatedAt=1748048384467)
Business email scams work like this: a hacker gets into your email, swaps out your payment details for their own, and your customer sends money to the wrong account.
The FBI reported $2.8 billion lost to these scams in 2024. These attacks have gone up 1,760% since AI tools became easy to use. Small businesses get hit the hardest.
Simple Steps to Secure Your Billing
Use your FSM platform's built-in invoicing. It is encrypted and sent through a safe system, not personal email.
Use a secure payment tool like Square, Stripe, or your FSM's built-in payments.
If a customer says their bank account changed, call them to confirm before you update anything.
Set up email security rules (DMARC, DKIM, SPF) to stop criminals from sending fake emails that look like they came from you.
12. Build a Field Data Security Policy
A policy does not have to be long. For a small trades business, one page that everyone signs is enough.
Cover the basics:
-
Which devices are approved for work
-
How techs must lock and protect their devices
-
What data can be shared and how
-
What to do if a device is lost
-
Who to call if something looks wrong
What happens when someone leaves: cut access, wipe devices, change passwords that same day
Review it once a year. Threats change fast.
13. What to Do If a Device Is Lost or Stolen
Speed matters. Every minute is a minute someone could be reading your customer data.
Your Response Checklist
Step 1: Use your MDM app to wipe the device right away.
Step 2: Change all passwords linked to that device.
Step 3: Log out of all active sessions on every business app.
Step 4: Check your access logs to see what data the device used in the last 24 to 48 hours.
Step 5: If customer data may have been seen, notify those customers. US state laws and Canada's PIPEDA may require it.
Step 6: Report to your cyber insurer if you have a policy.
Write this down and make sure at least two people know exactly what to do.
14. Know Your Legal Duties Around Customer Data
This is not just a security issue. It is a legal one.
In the US, all 50 states have laws that require you to tell customers if their data is exposed. If you fail to do so in time, you can face fines and lawsuits.
In Canada, PIPEDA covers every private business, no matter the size. If personal data is exposed, you must report it to the Privacy Commissioner and tell the affected customers. Fines can reach $100,000.
The FTC also sets data rules across the US. The Safeguards Rule requires businesses that handle financial data to have a written security plan.
15. Consider Cyber Insurance
Only 17% of small businesses have cyber insurance. But the average claim for a small business is $79,000, and the average ransom payment hit $3.6 million in 2024.
Cyber insurance covers breach costs, ransom payments, customer notice, lost business time, and legal fees. For trade contractors, plans often start at around $145 per month.
There is also a bonus: insurers require you to have good security in place before they will cover you. Getting insured pushes you to fix the things that matter most.
16. What Is Coming Next in Field Data Security
Technology moves fast. Here is what field service businesses need to watch:
-
AI-powered phishing: criminals now use AI to write scam emails that look exactly like real ones. The old advice of 'check for spelling errors' no longer works.
-
Smart building risks: HVAC techs are connecting more and more to smart building systems. Many of these systems have no built-in security. Every smart thermostat could be a way in. Always keep these networks separate from your main business network.
-
Zero Trust security: this means no device or user is trusted by default, even inside your own network. As fieldwork goes more digital, this approach is becoming the standard even for small businesses.
-
SASE (Secure Access Service Edge): Most security systems send your data through a central server before it reaches your tech's phone or tablet. SASE skips that step. It protects data right at the device, wherever your tech is - on a job site, in a driveway, or on the road. Your team gets a faster, safer connection without needing a VPN. More FSM software companies are starting to add this, so ask your provider if they support it.
The best way to stay ahead: review your security once a year and train your team often.
Final Thoughts
Your customers trust you with their homes, their businesses, and their data. That trust is worth protecting.
You do not need a full IT team to do this right. You need a VPN, two-step login, personal logins for each tech, MDM software, and a team that knows what to look for. That is your foundation.
Build on it with a cloud-based job management platform like Field Promax that handles data security at the system level. When your schedule, invoices, work orders, and customer records all live in one safe, access-controlled system, you cut out most of the risk.
Frequently Asked Questions
Reviewed by

Content Creator
Bhargavi Halthore is a content writer at Field Promax, a field service management platform serving trades businesses across the USA and Canada. With over a decade of experience writing for business owners, she brings detailed, ground-level insight to every topic she covers. Her research goes beyond search results - she digs into LinkedIn groups, Facebook communities, and Reddit forums to understand what field service business owners are actually dealing with on the ground. She speaks directly with industry professionals, understands their day-to-day challenges, and translates that into content that is practical and actionable. What you read in her articles reflects real industry patterns, not theory.
